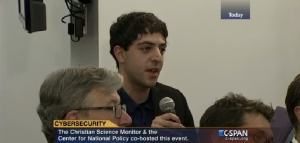
Recently the Lab sent member Aaron Alva to Washington DC (from one Washington to another!) to attend a cybersecurity event co-hosted by the Center for National Policy and the Christian Science Monitor. The event included a Q&A with the White House cybersecurity coordinator Michael Daniel, and a panel with experts including DEF CON founder Jeff Moss.
In the below post, Aaron highlights key takeaways from the event, specifically from the White House coordinator.
Mr. Daniel shared a few key areas that will be important to our nation’s cybersecurity progress in the future:
- Cybersecurity is a hard policy problem;
- the cybersecurity workforce needs to grow—in numbers, skills, and disciplines;
- the White House will attempt piecemeal legislation for cybersecurity since wholesale bills haven’t worked; and
- the National Institute of Standards and Technology (NIST) Cybersecurity Framework, while voluntary, is important and will be emphasized by the White House.
Mr. Daniel had some insightful comments on cybersecurity as a policy issue. He noted that cybersecurity is emerging as one of the defining policy challenges for the 21st century, yet it is not obvious why cybersecurity is such a difficult problem. Cybersecurity could be an easy problem. It could be ensuring that everyone patches vulnerabilities so that intruders cannot get into systems. But, taking a step back, cybersecurity is difficult because it cuts across social, private, and public lives. Mr. Daniel asserted that cybersecurity is not merely a technical problem—it is also an economic, political, and human behavior problem. It is a “wicked problem.” It is a problem that will take a wide variety of disciplines to help solve.
Second, Mr. Daniel emphasized the need for a cybersecurity workforce. His idea of a cybersecurity workforce encompasses two main themes—size and diversity of skills. Mr. Daniel noted that the workforce needs to be much bigger. He referenced government initiatives to increase workforce size. These initiatives include increasing the number of university Centers of Excellence in Information Assurance (UW is a Center of Excellence in Academics & Research). They also include growing the NSF CyberCorps scholarship program (of which I am a recipient). Mr. Daniel also described the need for more diverse skills for the cybersecurity workforce. He referenced the National Initiative for Cybersecurity Education (NICE initiative), which has developed a heatmap of cybersecurity roles necessary for a robust workforce. He noted that cybersecurity careers need to include individuals who understand how cybersecurity interacts with industries, businesses, and the law.
Third, the White House cyber czar briefly described his role as coordinator, and his new approach to cybersecurity legislation. He described his role is as a soft power in the White House. His goal is to align policy within the government bureaucracy. Mr. Daniel asserted that cyber is too big to put one person in charge, and the more appropriate role for the White House cyber coordinator is to get various agencies to coordinate.
Mr. Daniel also emphasized the need for cybersecurity legislation, and that legislation was long overdue. He stated that the White House will try a new approach. The White House will work to pass pieces of cybersecurity legislation however possible. The new piecemeal approach is in contrast to the typical approach of attempting to pass cybersecurity legislation all within a single bill.
Fourth, Mr. Daniel discussed the NIST Cybersecurity Framework. The Framework was developed by NIST by direction of an Executive Order from the White House. The Framework emphasizes that organizations should use risk management practices for cybersecurity through five categories. Organizations should Identify assets to secure; Protect those assets in a manner consistent with risks; Detect attacks; Respond efficiently after an incident to mitigate harm; and Recover from an incident.
Mr. Daniel believes that the Framework should be voluntary, but stressed that the US has a long history of effective voluntary standards. He noted that ultimately market forces will push the Framework forward. In a number of questions, Mr. Daniel referred back to the Framework’s main categories to emphasize the need for organizations to use risk management practices to deal with cybersecurity issues.
Finally, as part of the Q&A, I had the opportunity to ask Mr. Daniel a question. I asked what can be done to change the conversation from fear of being breached to one more realistically tailored to the fact that breaches will occur. I referenced recent headline breaches of Target, JPMorgan Chase, Home Depot, and others. I noted that these headlines primarily focused on the incident itself, rather than what the companies did in response to being attacked. His answer was telling, and I think he was correct. Mr. Daniel used the NIST Cybersecurity Framework to illustrate that there’s a missing part to the conversation. “But what [the NIST Cybersecurity Framework] is really saying is you got to actually figure out what information you have that you care about, and why do you care about it? What do you actually want to protect it from? Is it exposure at all? Or is it that you want to protect it from manipulation, that’s your greatest concern. And so that starts to define how you think about it and how you protect it, which is that second step.” See the full exchange here.
In conclusion, the White House cybersecurity coordinator provided helpful insights into the executive branch’s approach to cybersecurity. Mr. Daniel’s emphasis on the policy challenges, workforce needs, legislation, and risk management practices show a White House that desires to engage on a number of cybersecurity issues. Mr. Daniel remained optimistic that progress can be made on these issues, and that itself was welcomed news to the DC audience.